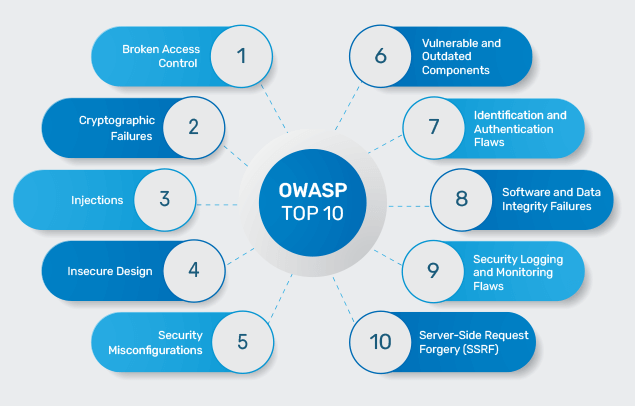
Web security can seem daunting, but it doesn’t have to be! The OWASP Top 10 is a list of the most critical web application security risks, created by the Open Web Application Security Project (OWASP). Let’s break down these top 10 security threats in a way that’s easy to understand. For those looking to deepen their understanding, consider enrolling in Asfela Academy’s application security training courses to gain hands-on knowledge.
1. SQL Injection
Think of SQL injection like someone shouting gibberish in a conversation, confusing the listener. This happens when untrusted data is sent to a database interpreter as part of a command or query, allowing attackers to manipulate the database.
How to prevent it: Use prepared statements and parameterized queries to separate data from commands. To master these techniques, application security courses often cover SQL injection prevention in detail.
2. Broken Authentication
This is like leaving your house keys under the doormat. Weak authentication systems allow attackers to easily gain unauthorized access to your web application.
How to prevent it: Implement multi-factor authentication, use strong, unique passwords, and limit failed login attempts. OWASP training often includes modules on securing authentication mechanisms.
3. Data Breach
Imagine sending a postcard with your personal details written on it. If your website doesn’t properly protect sensitive information (like credit card numbers or personal data), it’s vulnerable to data breaches.
How to prevent it: Encrypt sensitive data at rest and in transit, use strong encryption algorithms, and ensure secure storage. Application security training often emphasizes the importance of data protection.
4. XXE Attack
This is like having an open backdoor to your data. XML External Entity (XXE) attacks occur when XML processors allow external entities to be included, which attackers can exploit to access internal files or services.
How to prevent it: Disable external entity processing and use less complex data formats like JSON if possible. Web application security courses typically cover the prevention of XXE attacks.
5. Access Control Vulnerabilities
Access control is like having locked doors to certain rooms in your house. When access control is broken, unauthorized users can gain access to restricted areas.
How to prevent it: Enforce proper access controls by ensuring that users can only access the data and functions they’re authorized to. OWASP training for developers often includes best practices for implementing access control.
6. Security Misconfiguration
This is like setting up your home security system but forgetting to turn it on. Misconfigurations can happen at any level of an application stack, from the network to the web server, database, or framework.
How to prevent it: Regularly review and update configurations, and automate processes to deploy secure settings. Many application security training courses provide insights into avoiding common misconfigurations.
7. Cross-Site Scripting (XSS)
Imagine you’re reading a newspaper and it suddenly starts showing messages from someone else. XSS allows attackers to inject malicious scripts into web pages viewed by other users.
How to prevent it: Validate and sanitize user input, and use frameworks that automatically escape XSS. Learning how to prevent XSS is a key component of most web application security training programs.
8. Insecure Deserialization
This is like receiving a seemingly harmless package that contains something dangerous inside. Insecure deserialization occurs when untrusted data is used to manipulate an application’s logic, causing it to behave unexpectedly.
How to prevent it: Avoid deserialization of untrusted data, or use techniques like digital signatures to ensure the data hasn’t been tampered with. OWASP courses often cover the risks and mitigation strategies for insecure deserialization.
9. Using Outdated Components
It’s like building a house with bricks you know are faulty. Using outdated components (libraries, frameworks, etc.) with known vulnerabilities exposes your application to risks.
How to prevent it: Keep components up to date, and use tools to scan for vulnerabilities in your dependencies. Web application security training typically includes how to manage and update components securely.
10. Lack of Logging and Monitoring
Imagine your house is being broken into, but your security cameras aren’t recording. Without proper logging and monitoring, you might not detect a breach until it’s too late.
How to prevent it: Implement comprehensive logging of all activities and regularly monitor logs for suspicious behavior. Many application security training courses stress the importance of logging and monitoring as part of a robust security strategy.
By understanding the OWASP Top 10 vulnerabilities, you can significantly enhance your web application’s security. Remember, staying informed and proactive is the key to keeping your web presence safe! Consider taking Asfela Academy’s OWASP training, application security training courses, or a web application security course to gain the knowledge and skills needed to defend against these threats.


